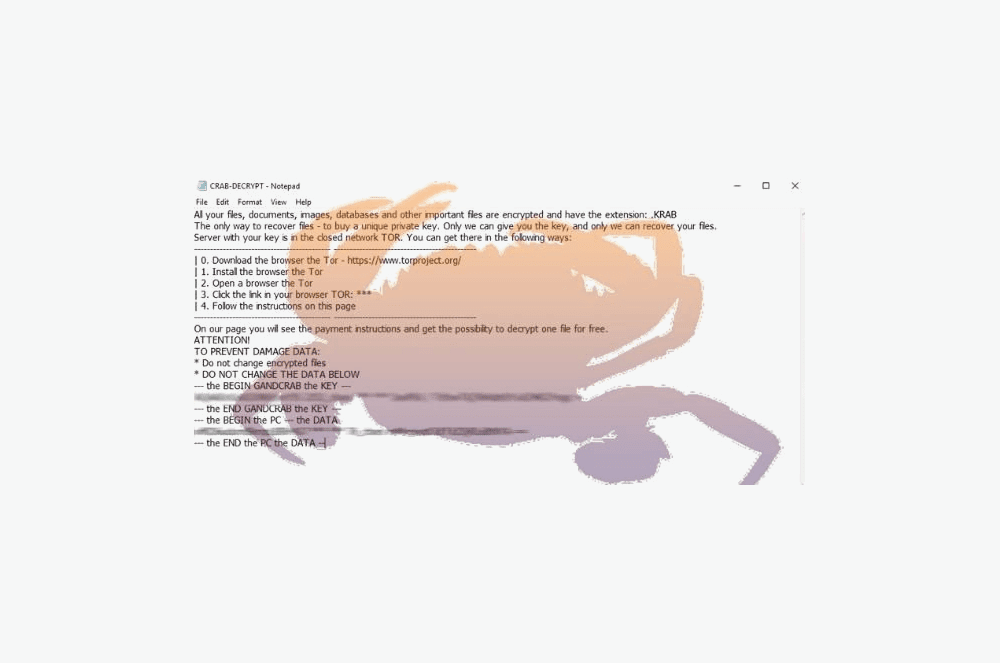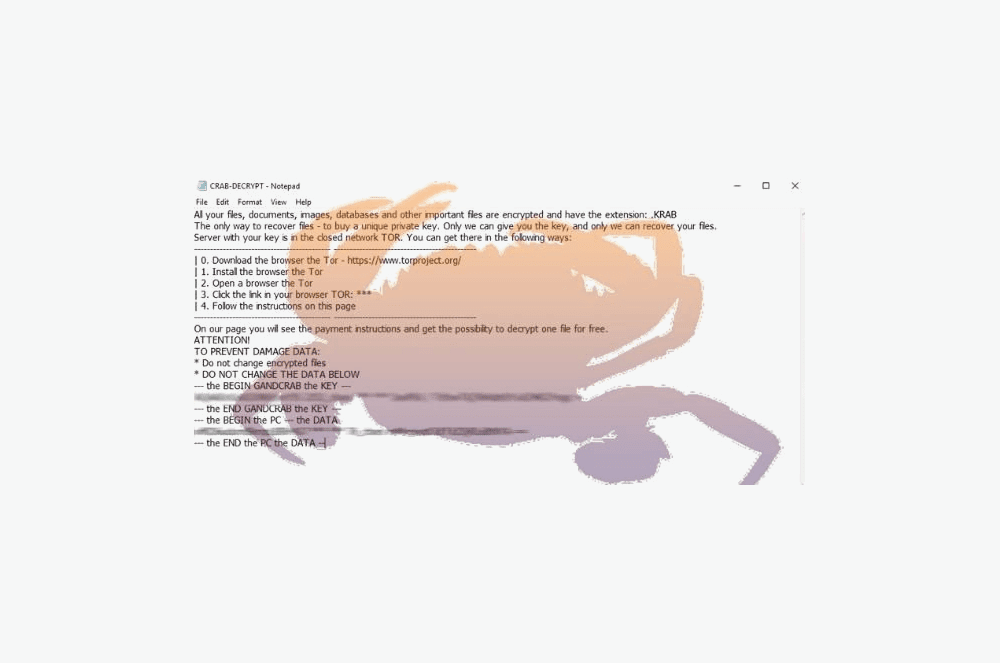
Ransomware Attack on a Newcastle Business
How the Attackers gained access to the Network
- The target computer was an old Computer used in the company workshop for product configuration.
- The workshop computer was kept connected to the Company Network and so provided a gateway into the LAN.
- The workshop computer had Windows default passwords for login. ( Who would want to Hack that old computer, right?)
- Once inside the workshop computer, the attackers were able to reach the company server and all other workstations plugged into the Company LAN.with the encryption ransomware. In some cases, workstations were encrypted by the ransomware whilst turned off
How the incident was resolved
- Fortunately the Company had moved to a Cloud Based solution for key Accounting and Sales systems, and these systems were unaffected.
- The Email and Company LAN files were backed up every night at close of business.
- The Email and Company LAN Files before the attack were restored and then all transactions since the attack were re-entered. In some cases this meant that customers need to be re-contacted and asked to re-send emailed Purchase orders, enquiries etc
- Workstations needed to be re-built and some data from workstations was non-recoverable
- The permanent connection that the Workshop computer had to the Company LAN was disabled and a server connection was only able to be made as and when required.
- The default passwords were changed on The Workshop Computer.
- Business disruption was minimal